Automotive Cybersecurity Timeline
The Internet has become a vital service for the operation of modern society, as important as energy distribution, water supplies, transportation infrastructure, and telecommunications networks. The Internet is spreading into all the devices we use, our houses are becoming smarter, and the cars we drive are connected. However, as the previous decades of office-based information technology (IT) have shown, if something is connected to the Internet, it becomes a target. Hackers probe the Internet to find exploitable weaknesses in the software and hardware that run the connected devices. This applies to the connected car; if a car is connected to the Internet, then the car's systems need to be secure and able to withstand attack attempts. This article explores automotive cybersecurity in the form of a timeline. It traces back from recent research into automotive hacking to the beginning of the technology that enabled the emergence of the connected car. Reading this automotive cybersecurity timeline will provide a sense of the importance of vehicle cybersecurity research and the technological advances that enabled the concept of connected cars.

A List of Events Related to Vehicle Hacking
Car hacking has occurred ever since digital electronics appeared in vehicles. Starting with chipping engine Electronic Control Units (ECUs) for more engine power and using laptops to alter digital odometers, through to researchers proving that unaltered cars can be hacked remotely over the Internet. This timeline, from the latest to the earliest, on car hacking looks at the key technologies and events that brought about the computerised car and how it can be hacked. If you have a suggestion for the timeline please send an email to dan@tekeye.uk.
August 2025 - Hyundai wants Ioniq 5 owners to pay to fix a keyless entry security hole - Car manufacturers have been fixing their systems to lock out a "Gameboy" hacking device for vehicles (see July 2020 below). Despite improving the security in production vehicles, Hyundai wants existing Ioniq 5 owners to pay for a retrofit.
https://www.theverge.com/news/757205/hyundai-ioniq-5-security-upgrade-fix-game-boy-device-attacks
August 2025 - Researcher Deploys Fuzzer to Test Autonomous Vehicle Safety - Security testing must be part of any connected product or system testing. Fuzz testing has been one technique security testers have used for a long time. It is now been used to test malicious teleoperation commands for autonomous vehicles.
https://www.darkreading.com/cyber-risk/researcher-deploys-fuzzer-to-test-autonomous-vehicle-safety
July 2025 - Tesla is granted US Federal Communications Commission (FCC) permission to simulate radio frequency attacks. This allows Tesla to test the cellular hacking resilience of its vehicles and new robotaxis. Nearly all hacking is performed remotely, and cellular communication is present in most of the mass-market vehicles being designed and manufactured by the big automakers. It makes sense for manufacturers to test vehicle resilience against hacking.
https://uk.pcmag.com/ai/159226/tesla-is-testing-if-malicious-actors-can-remotely-hack-its-robotaxis
July 2025 - Security vulnerability on U.S. trains that let anyone activate the brakes on the rear car was known for 13 years. As has been shown with a few of the other links below, it is not only cars that can be compromised by hacking. In this case, US trains have had a weakness for some time.
June 2025 - North American airlines targeted by cyberattacks - Anything with connectivity is a cyber target. Cars are just part of the transportation systems we rely upon.
June 2025 - Smart Tractors Vulnerable to Full Takeover - Tractors are vehicles, and have used computer systems for a while; security is not always addressed.
https://www.darkreading.com/cloud-security/hackers-hay-smart-tractors-vulnerable-takeover
June 2025 - Tesla Wall Connector Charger Hacked Through Charging Port - Tesla had to introduce a block to firmware downgrades for their wall-mounted chargers after researchers discovered a vulnerability. The hack potentially allowed Tesla wall chargers to become a pivot point for wider network intrusion.
https://cybersecuritynews.com/tesla-wall-connector-charger-hacked/

June 2025 - Extracting privacy-sensitive information via forensic analysis of a Mercedes-Benz infotainment system. Researchers demonstrate the extraction and use of GPS data and other information from a vehicle's infotainment system.
https://www.sciencedirect.com/science/article/pii/S2666281725000484
May 2025 - Hacking My Car, and probably yours - Security Flaws in Volkswagen’s App - Weaknesses in the VW phone app reveal weak security, data exposure, and privacy issues.
December 2024 - We know where your car is - The Chaos Computer Club reveals that Volkswagen, via its Cariad software subsidiary, is storing a mass of highly sensitive data insecurely on the Internet, data collected by VW cars. The issue is reported in a Speigel article and raised in the European Parliament.
https://www.ccc.de/en/updates/2024/wir-wissen-wo-dein-auto-steht
October 2024 - Keyless car thieves who stole high-value cars worth £2million across London (including one that had a three-year-old boy sat inside) using a device disguised as a "Gameboy" (see July 2020 below) are jailed for 13 years.
August 2024 - Hacking Digital License Plates with Fault Injection - IOActive's Josep Pi Rodríguez presented on a hack to allow a digital license plate to be changed via a phone's Bluetooth connection. This opens up a method to evade toll and parking charges. A Popular Science article in December describes the hack.
https://www.popsci.com/technology/digital-license-plates-hacked/
June 2024 - Researchers warn robot cars can be crashed with tinfoil and paint daubed on cardboard - American researchers perform a sensor attack that could be used to confuse automated vehicles.
https://www.theregister.com/2024/06/03/baidu_robotaxi_attack/
May 2023 - Hyundai and Kia agree to $200 million settlement over TikTok car theft challenge - A simple physical hack of Kia and Hyundai ignition systems using a USB connector led to an increase in thefts and a subsequent consumer class-action lawsuit settlement worth $200 million.
https://www.theverge.com/2023/5/18/23729229/hyundai-kia-settlement-car-theft-challenge-tiktok
April 2023 - CAN Injection: keyless car theft - Ken Tindell documents how a vehicle Controller Area Network (CAN) system flaw allows the vehicle to be stolen by hacking into vehicle wiring. For example, how thieves accessed the CAN bus via the front headlight wiring loom after snapping off front bumper fittings.
https://kentindell.github.io/2023/04/03/can-injection/
March 2023 - Pwn2Own Hackers Breach a Tesla (Twice), Earn $350K and a Model 3 - The ethical hackers' favourite car target, Tesla, is breached again to earn bug bounties.
https://uk.pcmag.com/security/146111/tesla-hacked-twice-at-ethical-hacking-conference
January 2023 - FAA outage: US airline regulators blame contractor for travel chaos - When travel chaos happens because of a computer failure, it can be assumed that a system was hacked. However, a careless engineer can cause similar issues.
https://www.bbc.co.uk/news/world-us-canada-64341873
January 2023 - Security Researchers Say They Hacked California's Digital License Plates, Because Duh - Gizmodo provides some more background on ethical hackers breaking the Reviver RPlate electronic vehicle number plate system.
https://gizmodo.com/security-researchers-hack-reviver-digital-license-plate-1849967297
January 2023 - Web Hackers vs. The Auto Industry: Critical Vulnerabilities in Ferrari, BMW, Rolls-Royce, Porsche, and More - Ethical hacker Sam Curry lists all the auto manufacturers' apps and application programming interface (API) issues he has found.
https://samcurry.net/web-hackers-vs-the-auto-industry/
November 2022 - Researchers find bugs allowing access, remote control of cars - Ethical hackers find weaknesses within vehicle apps and applications programming interfaces (APIs) to breach connected vehicle systems. Researcher Sam Curry later documents more automotive-related issues in a January 2023 blog post, see above.
https://therecord.media/researchers-find-bugs-allowing-access-remote-control-of-cars/
October 2022 - You Can't See Me: Physical Removal Attacks on LiDAR-based Autonomous Vehicles Driving Frameworks - Researchers use a laser-based spoofing technique to remove objects being detected by vehicles' LiDAR-based sensors.
https://www.usenix.org/conference/usenixsecurity23/presentation/cao
August 2022 - Gone in 130 seconds: New Tesla hack gives thieves their own personal key - A researcher finds a weakness in the Tesla NFC key card usage to clone the car on a mobile phone and use it to steal the car.
May 2022 - Review of Electric Vehicle Charger Cybersecurity Vulnerabilities, Potential Impacts, and Defenses - Researchers publish a paper listing the many security issues with EV chargers that have been discovered.
https://www.mdpi.com/1996-1073/15/11/3931
May 2022 - Reversing Kia Motors Head Unit to discover and exploit software vulnerabilities - Researchers document how they find potential vulnerabilities in a vehicle infotainment unit.
https://link.springer.com/article/10.1007/s11416-022-00430-5
February 2022 - University of Oxford and armasuisse S+T researchers can instantaneously stop multiple electric vehicles (EVs) from charging using electromagnetic interference (radio waves). Their Brokenwire attack is against the common Combined Charging System (CCS) of direct current (DC) rapid chargers for EVs. The attack disrupts and breaks charging communications between the EV and the charger to abort a charging session. The attack is wireless and is conducted from a distance.
January 2022 - Security failures in an open source app for Tesla users enabled researcher, David Colombo to access the functions of Teslas owned by others in disparate locations.
August 2021 - The joint ISO and SAE international standard ISO/SAE 21434:2021 Road vehicles - Cybersecurity engineering is published.
https://www.iso.org/standard/70918.html
August 2020 - The Big Tesla Hack: A hacker gained control over the entire fleet, but fortunately he’s a good guy - An article covers how a Tesla enthusiast found flaws in Tesla systems.
https://www.iso.org/standard/70918.html
July 2020 - This $25,000 'Game Boy' Is Made For Stealing Cars, Not Playing Tetris - A report from The Drive discusses a new tool to decode vehicle signals and enable vehicle access without a key. The device is styled similar to an old Gameboy.
https://www.thedrive.com/tech/34817/this-25000-game-boy-is-made-for-stealing-cars-not-playing-tetris
June 2020 - The UNECE World Forum for Harmonization of Vehicle Regulations (WP.29) issued vehicle regulations on a Cyber Security Management System (CSMS) and on vehicle software updates.
https://unece.org/fileadmin/DAM/trans/doc/2020/wp29grva/ECE-TRANS-WP29-2020-079-Revised.pdf https://undocs.org/ECE/TRANS/WP.29/2020/80
March 2020 - Keen Security Lab used a multistage attack to achieve a compromise of a Lexus vehicle and transmit Controller Area Network messages that can perform potentially dangerous actions.
January 2020 - Using an image projector it is possible to fool camera-based Advanced Driver Assistant (ADAS) systems into believing a ghost object, road marking or a person is present in front of the vehicle.
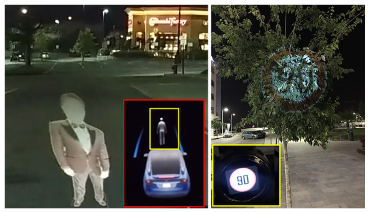
https://www.nassiben.com/phantoms
November 2019 - Using Bluetooth Low Energy (BLE) as a vehicle identifier can lead to privacy and tracking issues, so Have a Tesla Model 3? This app can track its location.
https://the-parallax.com/2019/11/14/tesla-radar-model-3-phone-key-ibeacon/
November 2019 - Man pleads guilty to stalking and controlling ex-girlfriend's car with his computer
September 2019 - As physical security is displaced by computer-controlled security, a computer issue can affect lots of vehicle owners at once, as when Tesla Owners Locked Out of Cars on Labor Day When Phone Key App Goes Down.
https://www.caranddriver.com/news/a28904319/tesla-owners-locked-out-of-cars-phone-key/
April 2019 - Fleet management apps are cracked, allowing data from thousands of accounts to be obtained and the potential immobilisation of thousands of vehicles.
See: https://www.vice.com/en_us/article/zmpx4x/hacker-monitor-cars-kill-engine-gps-tracking-apps
May 2019 - Despite all the publicity on key fob relay hacks, they are still a weakness in vehicle security, and this hack could take control of your Ford.
https://the-parallax.com/2019/05/03/hacker-ford-key-fob-vulnerability/
December 2018 - PAS 1885:2018, The fundamental principles of automotive cyber security. Specification - Published by the British Standards Institute (BSI), it builds upon the UK Government's guidelines published in 2017.
https://shop.bsigroup.com/ProductDetail/?pid=000000000030365446
November 2018 - CarsBlues, A vehicle Bluetooth hack that exploits infotainment systems to allow for access to call logs, text messages and other private data.
https://www.privacy4cars.com/can-my-car-be-hacked/
May 2018 - Researchers find vulnerabilities in BMW head units and telematics ECUs using fake GSM base stations.
April 2018 - Dutch security researchers remotely access Volkswagen Group infotainment units made by Harman.
https://www.computest.nl/nl/knowledge-platform/rd-projects/car-hack/
August 2017 - The key principles of vehicle cyber security for connected and automated vehicles - The UK Government publishes cybersecurity guidelines for connected and automated vehicles (CAVs).

March 2017 - The WikiLeaks Vault 7 documents reveal that "As of October 2014 the CIA was also looking at infecting the vehicle control systems used by modern cars and trucks" and "The purpose of such control is not specified, but it would permit the CIA to engage in nearly undetectable assassinations."
September 2016 - Keen Security on Car Hacking Research: Remote Attack Tesla Motors
September 2016 - Your Car’s New Software Is Ready. Update Now? - The New York Times reports how remote updates of vehicle software are increasingly common. General Motors (GM) has been doing it with their OnStar system since 2009, and Tesla since 2012. The issue of security for those updates is raised.
https://www.nytimes.com/2016/09/09/automobiles/your-cars-new-software-is-ready-update-now.html
November 2015 - Hackers Cut a Corvette’s Brakes Via a Common Car Gadget
https://www.wired.com/2015/08/hackers-cut-corvettes-brakes-via-common-car-gadget/
September 2015 - EPA, Learn About Volkswagen Violations. The US Environmental Protection Agency issues a notice of Violation to the Volkswagon Group over the use of a software defeat device for emissions testing. The manufacturer’s hack affects vehicle models from 2009.
https://www.epa.gov/vw/learn-about-volkswagen-violations
2015 - Hackers remotely kill a Jeep on the highway – with me in it, Wired
https://www.wired.com/2015/07/hackers-remotely-kill-jeep-highway/
2015 - Markey, Blumenthal To Introduce Legislation to Protect Drivers from Auto Security and Privacy Vulnerabilities with Standards and "Cyber Dashboard", Senator Edward Markey
July 2015 - Markey Report Reveals Automobile Security and Privacy Vulnerabilities, Senator Edward Markey
2015 - Hackers Can Take Control of Cars From 3,000 Miles Away, NBC 4 New York
https://www.nbcnewyork.com/news/local/hack-a-car-computer-wifi-remote-vehicle-hacking-291272611.html
2014 - A Survey of Remote Automotive Attack Surfaces
https://ioactive.com/pdfs/IOActive_Remote_Attack_Surfaces.pdf
2014 - Auto Alliance Initiates New Cybersecurity Forum, Automotive Information Sharing and Analysis Center
https://www.automotiveisac.com/
2014 - Most Hackable Cars, CNN Money
https://money.cnn.com/2014/08/01/technology/security/most-hackable-cars/index.html?hpt=hp_t2
2014 - The Robot Car of Tomorrow May Just Be Programmed to Hit You, Wired
https://www.wired.com/2014/05/the-robot-car-of-tomorrow-might-just-be-programmed-to-hit-you/
2014 - Open Garages
http://opengarages.org/index.php/Main_Page
2013 - Sen Markey (D-MA) Letter to GM
https://www.markey.senate.gov/documents/2013-12-2_GM.pdf
2013 - Jury Finds Toyota Liable in Fatal Wreck in Oklahoma, New York Times
https://www.nytimes.com/2013/10/25/business/jury-finds-toyota-liable-in-fatal-wreck-in-oklahoma.html
August 2013 - Adventures in Automotive Networks and Control Units, presented at DEF CON 21, PDF here.
https://www.theregister.co.uk/2013/06/25/miller_car_hacking/
2013 - Car Hacking Your Computer-Controlled Vehicle Could Be Manipulated Remotely, CBS
https://losangeles.cbslocal.com/2013/11/20/car-hacking-michael-hastings/
2013 - How to Hack Your Mini Cooper, Reverse Engineering CAN Messages on Passenger Automobiles, Jason Stags, Defcon 21
July 2013 - Researchers Charlie Miller and Chris Valasek control a Prius from a laptop; there are links to lots more car hacking videos in the Tek Eye article Car Hacking Videos
https://www.youtube.com/watch?v=oqe6S6m73Zw
July 2013 - It is alleged that the journalist Michael Hastings was killed via a car cyber-attack.
https://www.huffingtonpost.co.uk/entry/michael-hastings-car-hacked_n_3492339
September 2012 - UK Channel 4 News report on a, then, weakness in electronic car key fobs that allowed easy car theft.
https://www.youtube.com/watch?v=HuLKormzWE4
September 2012 - Korean researchers use a malicious Android app to control a car
https://news.sbs.co.kr/news/endPage.do?news_id=N1001370933
August 2012 - The first annual Cyber Auto Challenge takes place.
https://www.sae.org/attend/cyberauto/
2011 - Can Your Car be Hacked?, Car and Driver
https://www.caranddriver.com/features/a15124906/can-your-car-be-hacked-feature/
August 2011 - Comprehensive Experimental Analyses of Automotive Attack Surfaces, Center for Automotive Embedded Systems Security (CAESS)
February 2011 - Relay Attacks on Passive Keyless Entry and Start Systems in Modern Cars
2010 - Security and Privacy Vulnerabilities of In-Car Wireless Networks, A Tire Pressure Monitoring System Case Study, Rutgers, USC
https://cse.sc.edu/~wyxu/papers/TPMSUsenix.pdf
2010 - Experimental Security Analysis of a Modern Automobile, Center for Automotive Embedded Systems Security (CAESS)
http://www.autosec.org/publications.html
2010 - Hacker disables more than 100 cars remotely, Wired
https://www.wired.com/2010/03/hacker-bricks-cars/
2009 - The Spirit of Berlin was an autonomous vehicle project by Freie Universität Berlin, started in 2007 for participation in the DARPA Urban Challenge as Team Berlin (a joint team by the Freie Universität Berlin, Rice University, Fraunhofer IAIS, and industrial partners Micro-Epsilon, Berlin Sciences, IBM Germany, IBEO), drivable remotely by an iPhone
https://www.youtube.com/watch?v=oHDwKT564Kk
2009 - Google's Self-Driving Car Project (renamed Waymo in December 2016)
https://en.wikipedia.org/wiki/Waymo
July 2008 - EVITA (E-safety Vehicle Intrusion proTected Applications) was a European project investigating improved vehicle security that ran till December 2011.

https://www.evita-project.org/
2007 - At CanSecWest, RDS-TMC hacking is demonstrated: Satnav hacking made simple - Create your own traffic jam, bullfight or air raid, later demonstrated at BlackHAt and DEF CON 15
https://www.theregister.co.uk/2007/04/20/satnav_hack/
2007 - DARPA Urban Challenge

https://archive.darpa.mil/grandchallenge/
2005 - Defeating the security of RFID Chips in Car Keys and Gas Pump, Johns Hopkins University, Security Analysis of a Cryptographically-Enabled RFID Device
2005 - DARPA Grand Challenge

https://archive.darpa.mil/grandchallenge05/
2005 - Linux Bluetooth hackers hijack car audio – The Register reporting on the Bluetooth hack
https://www.theregister.co.uk/2005/08/02/car_whisperer/
2005 - Hacking the Hybrid Vehicle, Wired
https://archive.wired.com/science/discoveries/news/2005/11/69519
July 2005 - Vehicle audio eavesdropping and injection via Bluetooth using The Car Whisperer Linux software.
https://trifinite.org/blog/archives/2005/07/introducing_the.html
May 2005 - A Toyota vehicle was provided to F-Secure to prove that the Toyota and Lexus Bluetooth virus could not infect their vehicles. (Note the strange behaviour of the vehicle electronics at low battery levels. Could this ever be utilised to break a system?)
https://www.f-secure.com/weblog/archives/00000553.html
January 2005 - Unsubstantiated claims that Toyota and Lexus navigation systems can be infected with a computer virus via Bluetooth.
https://www.scmagazine.com/home/security-news/mobile-virus-infects-lexus-cars/
June 2004 - A Bluetooth proof-of-concept worm (virus) named SymbOS.Cabir is announced.
http://virus.wikidot.com/caribe
February 2004 - The NY Times article DRIVING; Altering Your Engine With New Chips discusses the pitfalls of changing the software in ECUs and some implications for vehicle damage.
https://www.nytimes.com/2004/02/13/travel/driving-altering-your-engine-with-new-chips.html
January 2004 - Chrysler offer Bluetooth in their UConnect telematics system (Intel X-Scale ARM CPU, Broadcom Bluetooth chipset, IBM ViaVoice software, and the QNX operating system).
https://www.pcmag.com/archive/the-bluetooth-car-117748
November 2003 Bluetooth vulnerabilities are published by security researchers Adam Laurie and Ben Laurie on bluestumbler.org (no longer available).
https://web.archive.org/web/20031118173621/http://www.bluestumbler.org/
September 2003 - In America, Acura TL (Honda) cars are equipped with Bluetooth.

https://en.wikipedia.org/wiki/Acura_TL#2004
October 2003 - The UK Government made the The Road Vehicles (Construction and Use) (Amendment) (No. 4) Regulations 2003 banning driving whilst using a mobile phone. Effectively mandating the use of hands-free kits and thus phone-to-car links.
https://www.legislation.gov.uk/uksi/2003/2695/made
October 2003 - Orange UK (now EE) partners with Smart Automobile to offer a Smart City Coupe with Bluetooth hands-free.
https://www.carpages.co.uk/smart/smart_orange_gets_smart_08_10_03.asp
May 2003 - Thailand's Finance Minister Suchart Jaovisidha is trapped in a BMW due to a malfunction of the vehicle's computer system.
https://www.theage.com.au/technology/computer-glitch-traps-thai-minister-in-bmw-20030513-gdgr7n.html
2003 - The NY Times story Gentlemen, Start Hacking Your Engines on ECU modifications and a full injection system control by a digital organiser (Palm Pilot).
https://www.nytimes.com/2003/01/09/technology/gentlemen-start-hacking-your-engines.html
August 2002 - A Forbes article How To Hack Your Car is on ECU programming. It includes comments on the lack of code security.
https://www.forbes.com/forbes/2002/0708/148.html
Start of the 2000s - The telematics solutions of ATX Technologies Inc., with Tele Aid, and General Motors with OnStar, have security weaknesses exposed (https://web.archive.org/web/20141023194256/http://silverstr.ufies.org/blog/archives/000455.html - Dana Epp - Security Expert) and are used for covert FBI surveillance.
https://www.theregister.co.uk/2003/11/20/court_limits_incar_fbi_spying/
1999 - The Mercedes S Class has Distronic, the World's first Adaptive Cruise Control (ACC) system (applying a brake as required), and the Pre-Safe collision and avoidance response system.
https://en.wikipedia.org/wiki/Autonomous_cruise_control_system
1999 - The first Bluetooth specification is released.
https://www.bluetooth.com/media/our-history
1999 - Anderson on hacking lorry tachographs, On the security of digital tachographs
https://link.springer.com/chapter/10.1007/BFb0055859
September 1997 - Intel Announces Connected Car Technology at IAA Frankfurt
At the Internationale Automobile Ausstellung (IAA) in Frankfurt, Germany, chip manufacturer Intel reveals its Connected Car PC:
"passengers in the Citroën Xsara are entertained by a DVD film with Dolby Surround Sound Stereo, while the RDS-Radio continually updates the driver with the latest traffic news. On request, the Connected Car PC picks up the travelers' incoming e-mail and, using a text to speech converter, reads it to them. Up to date information on weather, traffic and tourism can also be downloaded on demand by the Connected Car PC from the Internet"
https://www.intel.com/pressroom/archive/releases/1997/IC090997.HTM
1997 - General Motors Corporation offer Cadillacs with OnStar telematics.
https://en.wikipedia.org/wiki/OnStar#History
1996 - Only done 30,000. Honest, guv, car clocking has always been an issue, by using a laptop, digital odometers can be altered.
https://www.independent.co.uk/life-style/motoring/only-done-30000-honest-guv-1345479.html
October 1992 - Third generation Mitsubishi Debonair limousine came with the world's first Lidar-based distance warning.
https://en.wikipedia.org/wiki/Mitsubishi_Debonair#Third_generation
1987 to 1995 - The European Eureka PROMETHEUS Project (Programme for European Traffic of the Highest Efficiency and Safety) researched autonomous driving and related technologies with €749 million.
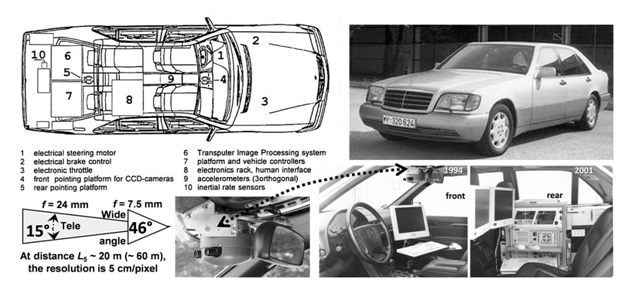
The 1980s - The early autonomous driving experiments using a Mercedes-Benz van equipped with machine vision led by Ernst Dickmanns.
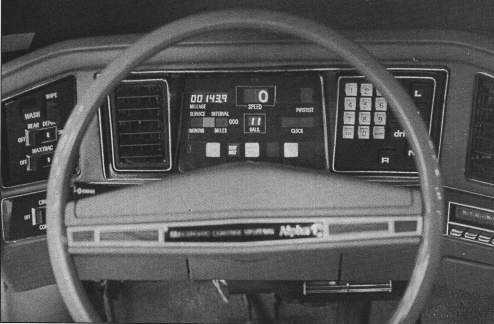
Mid-1970s - In the 1970's Aston Martin began incorporating digital electronics into their luxury Lagonda car, but the touch switches and LED displays only lasted until 1980 because of reliability issues.

Early 1970s - General Motors early computerised car experiments, The Feasibility of a Car Central Computer
https://www.sae.org/publications/technical-papers/content/730126/
1960s and 1970s - Early experiments in self-driving vehicles go back as far as the 1960s and originate from ideas for remote Moon missions.
1960s - ARPANET, from the Wikipedia article: The Advanced Research Projects Agency Network (ARPANET) was an early packet-switching network and the first network to implement the TCP/IP protocol suite. Both technologies became the technical foundation of the Internet.
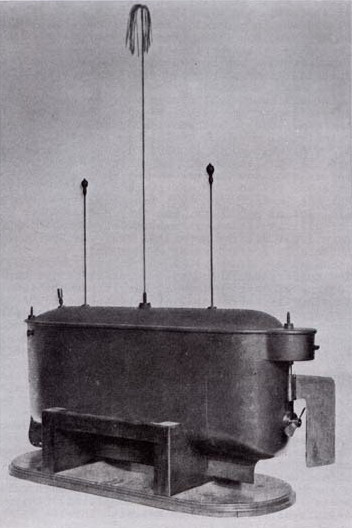
1930s and 1940s - The Soviet Union used remote-controlled tanks, the Teletank, during World War II.
1898 - Nikola Tesla's patent for a remote-controlled boat, Method of and Apparatus for Controlling Mechanism of Moving Vessels or Vehicles, demonstrated wireless command and control of a machine at the 1898 Electrical Exposition in Madison Square Gardens. This event is discussed in the thesis I, Robot: Nikola Tesla's Telautomaton.
See Also
- A list of Car Hacking Videos
- For a full list of all the articles in Tek Eye, see the full site Index
Author:Daniel S. Fowler Published: Updated:







